Organization-Owned Queries
Key benefit: Queries continue running even when the original creator is removed from the system or has their permissions changed.
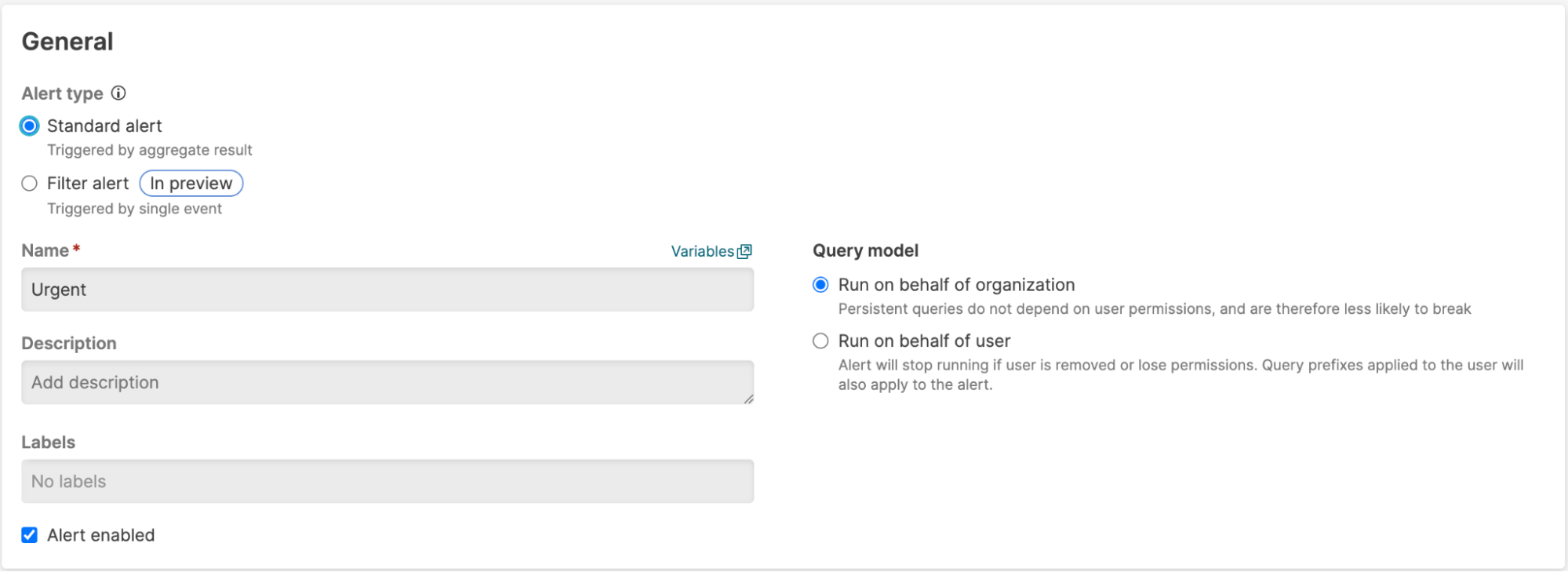
Organization-owned queries solve a common problem in LogScale deployments. Normally, queries run as the user who created them. This includes triggers, alerts, and shared dashboards. When the user who created one of these queries leaves the organization or loses permissions, their queries stop working. This results in query failures that can cause dependent actions and automated processes to fail.
Organization-owned queries provide a solution. Instead of running as an individual user, these queries run on behalf of the organization itself. This ensures continuous operation regardless of individual user changes.
Example scenario: You create an alert that uploads files when triggered. With standard user-owned queries, both the alert and file upload action fail if you leave the organization. With organization-owned queries, the alert continues working regardless of your employment status.
Organization-owned queries can be used for:
Organization-owned queries have these characteristics:
Persistent operation: Queries continue running even when their original creator is removed from the system.
Simplified permissions: No additional runtime permissions are required beyond the organization's existing access.
Restricted editing: Only users with organization query ownership permissions can modify these queries.
Permissions for organization-owned queries
To create, edit, or delete organization-owned queries in triggers you'll
need the permission Change persistent queries to run on behalf of organization. You must also have
this permission to create, edit, and delete scheduled reports.
Additionally, you must also have this permission to be able to edit an
action that is referenced by a trigger owned by the organization. In
general, you should not give this permission to anyone who is not already
able to see all data in the given view.
Organization query ownership is configured at the role level. Users
inherit this capability when assigned any role that includes the
organization query ownership permission. Additionally, users need the
View permission tokens
permission to create queries with organization ownership. This permission
is required because organization-owned queries use system-level
authentication tokens.
Activity logs for organization-owned queries
Organization-owned queries generate activity records in the
humio-activity and humio-audit repositories.
These records are tagged with the orgUser operation
type to distinguish them from regular user queries. The system uses
temporary authentication tokens (ephemeralUserToken) to
execute these queries.
Organization-owned queries and query prefixes
Organization-owned queries are incompatible with query prefixes applied to a group. A query prefix is a default search filter applied to queries for a given group. Enabling the organization-owned queries permission on a role applied to a group for a given view will require any configured query prefix to be removed.
When editing the group to remove a query prefix, select the role for the group and edit the query prefix, replacing it with either * or False as described:
 |
Then apply the permission on the role as described in Enable organization-owned queries for a role.
For more information about query prefixes, see Query prefix for roles assigned to groups.