Authenticate with OpenID Connect
LogScale supports authenticating with any provider following the
OpenID Connect standard.
When OpenID Connect (OIDC) is configured,
LogScale accepts OpenID tokens issued by the OpenID Connect provider
(LogScale acts as a resource in OpenID Connect terms). This is
useful if you are running LogScale behind a proxy that handles
authentication.
In addition to acting as a resource, LogScale can also act as a
client responsible for authenticating users (a relying party in OpenID
Connect terms). This is similar to other OAuth authentication flows
LogScale supports.
The diagram illustrates how OpenID Connect (OIDC) authentication works with
LogScale. LogScale can function in two roles within the OIDC
framework:
As a Resource where LogScale
accepts tokens issued by an OIDC provider
As a Relying Party (Client) where
LogScale handles authentication through an OIDC provider
sequenceDiagram
participant User
participant Browser
participant LogScale as LogScale
participant IDP as OIDC Provider
Note over User, IDP: LogScale as OIDC Relying Party (Client) Flow
User->>Browser: Attempts to access LogScale
Browser->>LogScale: Requests access to protected resource
LogScale->>Browser: Redirects to OIDC provider
Browser->>IDP: Redirects with client_id, redirect_uri, scope, etc.
IDP->>Browser: Presents login page
User->>Browser: Enters credentials
Browser->>IDP: Submits login credentials
IDP->>IDP: Authenticates user
IDP->>Browser: Redirects with authorization code to redirect_uri
Browser->>LogScale: Sends authorization code
LogScale->>IDP: Requests tokens with authorization code + client_secret
IDP->>LogScale: Returns ID token, access token, refresh token
LogScale->>IDP: Validates tokens & requests user info (if needed)
IDP->>LogScale: Returns user information
LogScale->>LogScale: Creates session & maps OIDC claims to user profile
Note right of LogScale: Maps username from claim<br>(configurable via OIDC_USERNAME_CLAIM)<br>Maps groups from claim<br>(configurable via OIDC_GROUPS_CLAIM)
LogScale->>Browser: Returns authenticated session
Browser->>User: Shows LogScale interface
Note over User, IDP: Alternative: LogScale as Resource (Token Validation Only)
User->>Browser: Attempts to access LogScale with token
Browser->>LogScale: Sends request with OIDC token
LogScale->>LogScale: Validates token signature using JWKS
LogScale->>LogScale: Verifies audience, issuer, expiration
LogScale->>LogScale: Extracts username & group info from claims
LogScale->>Browser: Returns authenticated session if token valid
sequenceDiagram
participant User
participant Browser
participant LogScale as LogScale
participant IDP as OIDC Provider
Note over User, IDP: LogScale as OIDC Relying Party (Client) Flow
User->>Browser: Attempts to access LogScale
Browser->>LogScale: Requests access to protected resource
LogScale->>Browser: Redirects to OIDC provider
Browser->>IDP: Redirects with client_id, redirect_uri, scope, etc.
IDP->>Browser: Presents login page
User->>Browser: Enters credentials
Browser->>IDP: Submits login credentials
IDP->>IDP: Authenticates user
IDP->>Browser: Redirects with authorization code to redirect_uri
Browser->>LogScale: Sends authorization code
LogScale->>IDP: Requests tokens with authorization code + client_secret
IDP->>LogScale: Returns ID token, access token, refresh token
LogScale->>IDP: Validates tokens & requests user info (if needed)
IDP->>LogScale: Returns user information
LogScale->>LogScale: Creates session & maps OIDC claims to user profile
Note right of LogScale: Maps username from claim<br>(configurable via OIDC_USERNAME_CLAIM)<br>Maps groups from claim<br>(configurable via OIDC_GROUPS_CLAIM)
LogScale->>Browser: Returns authenticated session
Browser->>User: Shows LogScale interface
Note over User, IDP: Alternative: LogScale as Resource (Token Validation Only)
User->>Browser: Attempts to access LogScale with token
Browser->>LogScale: Sends request with OIDC token
LogScale->>LogScale: Validates token signature using JWKS
LogScale->>LogScale: Verifies audience, issuer, expiration
LogScale->>LogScale: Extracts username & group info from claims
LogScale->>Browser: Returns authenticated session if token valid
Create an OpenID Connect app
Important
Prior to performing the steps below, make sure that you have a fully
activated Okta
account.
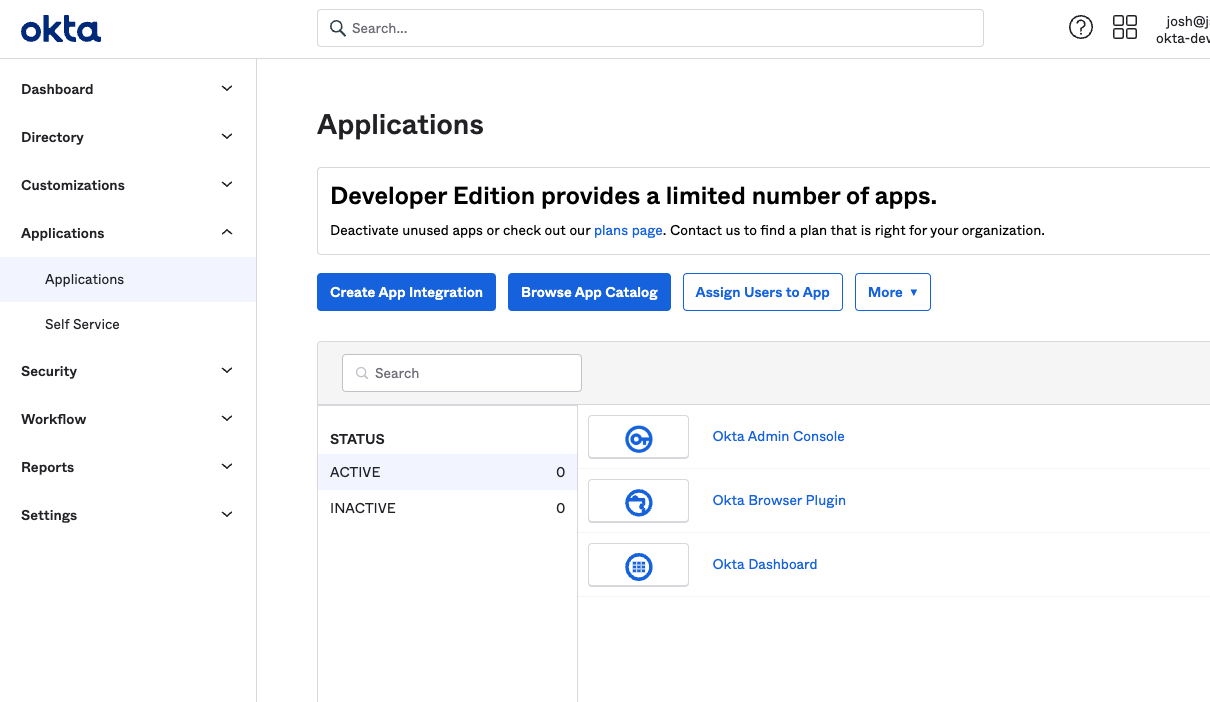
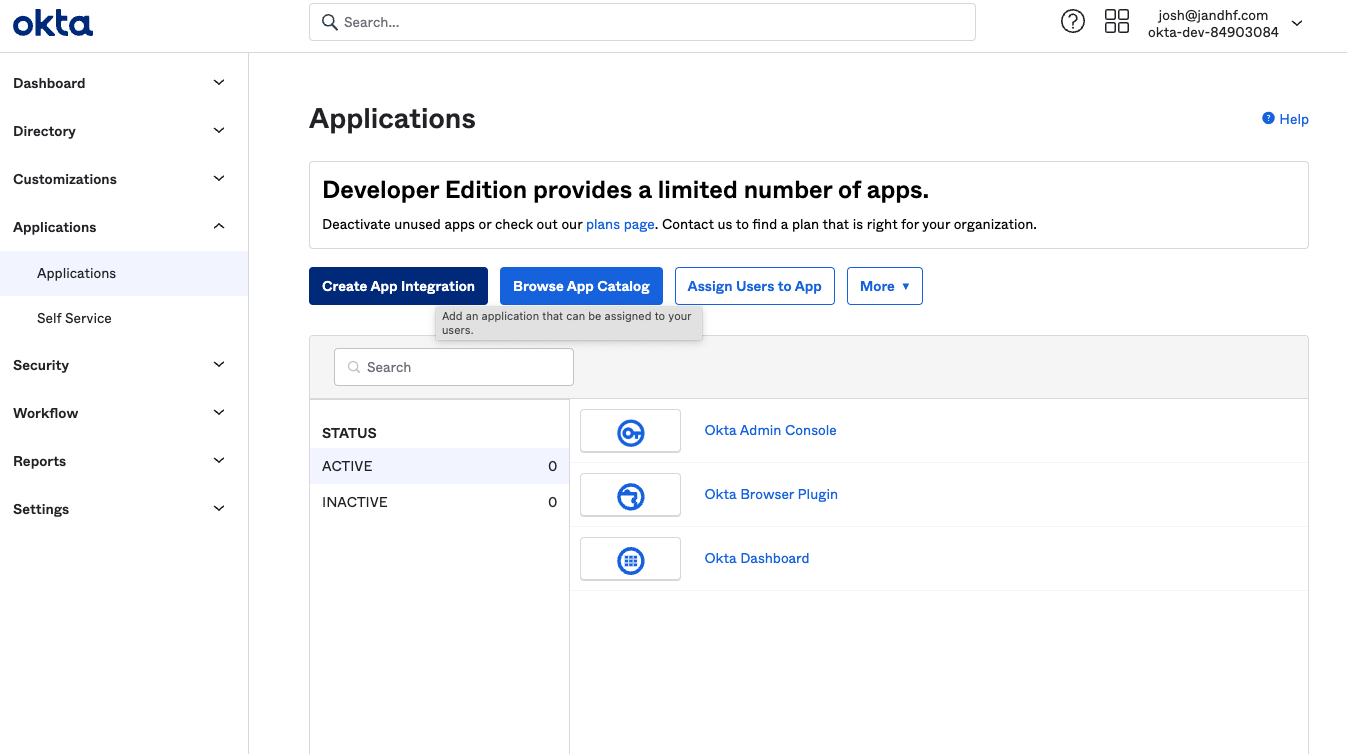
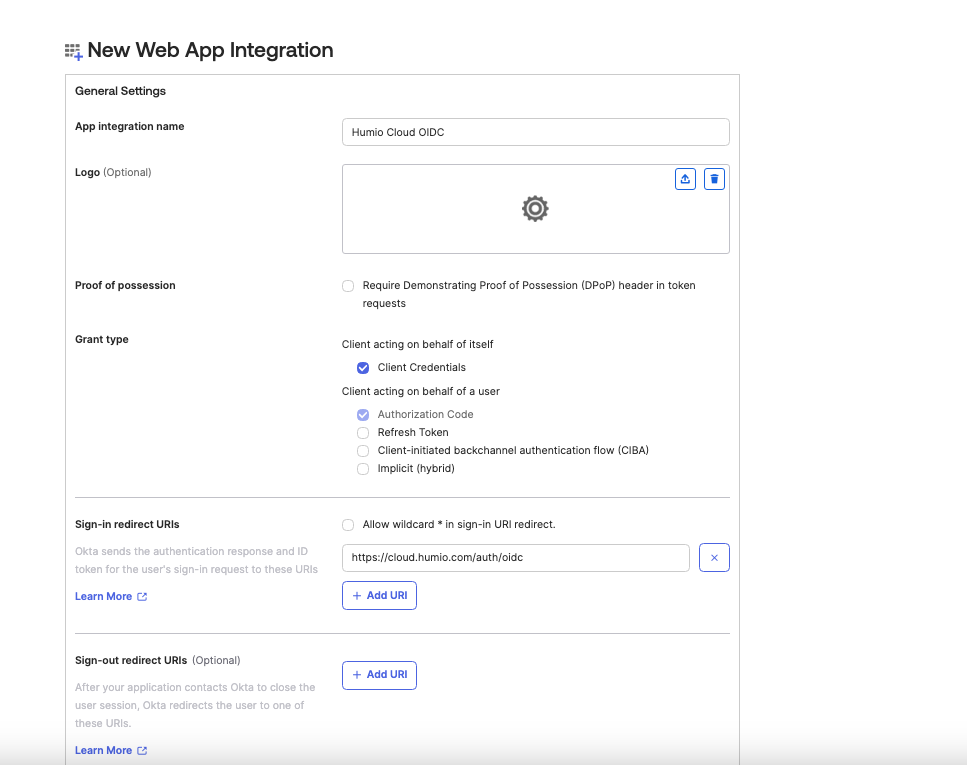
Log in and navigate to the main page of the Okta interface:
Click Adminto navigate to the
Admin Dashboard. From there,
click Applications and
select Applications.
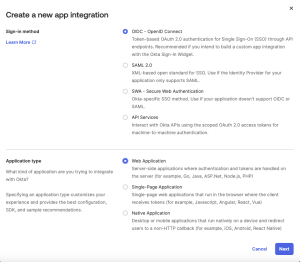
Next, click Create App
Integration.
Select OIDC - OpenID Connect
and Web Application. Click
Next.
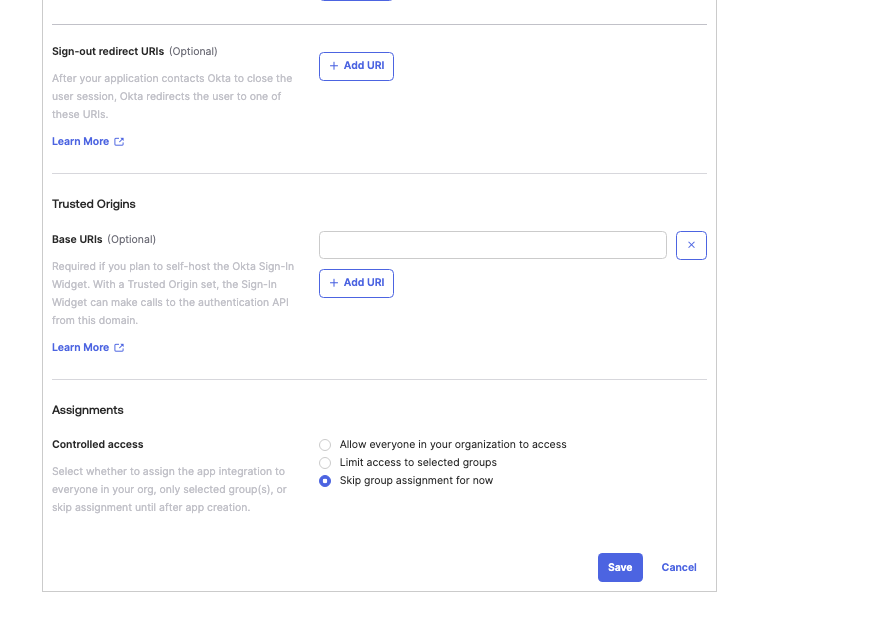
Name the app, for example LogScale OIDC, and upload an image
(optional). Enter the following:
Grant Type: Client
Credentials
Sign-in redirect URLs:
$LOGSCALE_URL/auth/oidc
Sign-out redirect URLs:
remove, if existing. Optional.
Assignments: Select Skip
Group Assignment for now
Click Save.
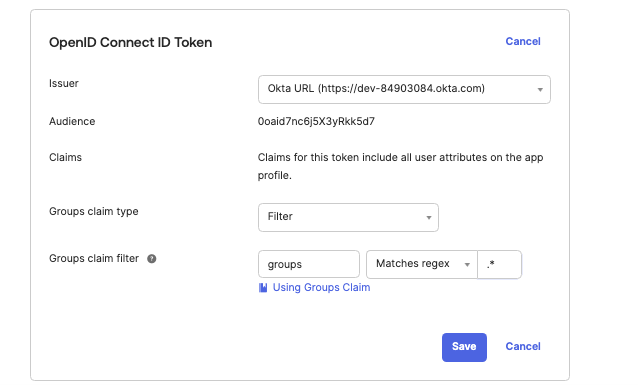
Click the Sign On tab of the
app, and under OpenID Connect ID
Token Set Issuer to
Okta URL (https://dev-84903084.okta.com). Set
Group claims filter to
groups and select
Matches regex with the regex pattern
.*. Click
Save.
Configure LogScale to use OpenID Connect
To configure OpenID Connect to work with LogScale,
contact Support.