
cisco/ise
| Vendor | Cisco Systems, Inc. | Parsers | ✓ |
| Author | CrowdStrike | Dashboards | ✗ |
| Version | 2.0.5 | Alerts | ✗ |
| Minimum LogScale Version | 1.207.0 | Actions | ✗ |
| Use Cases | ITOps SecOps | Scheduled Searches | ✗ |
| Supported Log Formats |
| ||
| Security Domain | Identity & Access Management Security |
| Field | Format | Timezone |
|---|---|---|
| @timestamp | yyyy-MM-dd HH:mm:ss[.SSSSSS] z | UTC |
| @timestamp | yyyy-MM-dd HH:mm:ss[.SSS] z | UTC |
| @timestamp | yyyy-MM-dd HH:mm:ss[.SSS] Z | UTC |
| event.created | MMM d HH:mm:ss z | UTC |
| event.created | MMM d HH:mm:ss | System default |
Cisco Identity Services Engine (ISE) is a next-generation NAC solution used to manage endpoint, user, and device access to network resources within a zero-trust architecture.
Cisco Identity Services Engine (ISE) is a security policy management and control platform. It facilitates the creation and enforcement of security and access policies across an enterprise network, helping to ensure that only authorized users and devices can access network resources.
It offers a range of features including authentication, authorization, and accounting (AAA), as well as device profiling, guest management, and posture assessment, among others.
Integrating Cisco ISE with LogScale can enhance the visibility and control over the security policies and activities within your network.
This package provides a parser for Cisco Identity Service Engine (ISE) events. It normalizes data to a common schema based on an OpenTelemetry standard. This schema allows you to search the data without knowing Cisco ISE's data specifically. It also enables you to combine the data more easily with other data sources which conform to the same schema.
Note: The initial release of this package focuses exclusively on IPv4 addresses and it parsers following ISE syslogs:
The full list can be found here. Parser should work for the other streams from that list as they follow the same log format however it was not tested.
The parser normalizes data to a common schema based on CrowdStrike Parsing Standard (CPS) 1.0. This schema allows you to search the data without knowing the data specifically, and just knowing the common schema instead. It also allows you to combine the data more easily with other data sources which conform to the same schema.
Breaking Changes
This update includes parser changes, which means that data ingested after upgrade will not be backwards compatible with logs ingested with the previous version.
Updating to version 1.0.0 or newer will therefore result in issues with existing queries in for example dashboards or alerts created prior to this version.
See CrowdStrike Parsing Standard (CPS) 1.0 for more details on the new parser schema.
Follow the CPS Migration to update your queries to use the fields and tags that are available in data parsed with version 1.0.0.
Installing the Package in LogScale
Find the repository where you want to send the events, or Creating a Repository or View.
Navigate to your repository in the LogScale interface, click Settings and then on the left.
Click and install the LogScale package for (i.e. cisco/ise).
In the right panel, click to create a new token. Give the token an appropriate name (the name of the event hub it will collect logs from), and leave the parser unassigned, you can assign the parser cisco-iseto the LogScale Collector Configuration as described in the documentation Configuration Examples.
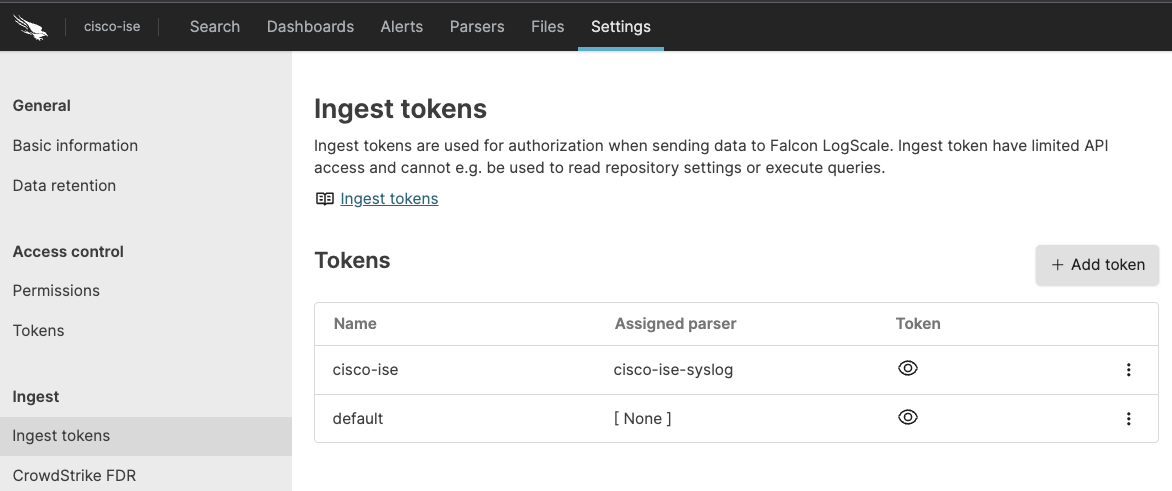
Figure 3. Ingest Token
Before leaving this page, view the ingest token and copy it to your clipboard — to save it temporarily elsewhere.
Now that you have a repository set up in LogScale along with an ingest token you're ready to send logs to LogScale.
Configurations and Sending the Logs to LogScale
First you need to configure Cisco ISE to send logs to the remote syslog server.
Sign in to Cisco ISE Portal and configure the Remote Syslog Collection Locations . Go to Administration — System — Logging — Remote Logging Targets and add remote server by providing below details:
Unique name for the remote target system
Description of your target system
IP Address of the remote syslog server
Insert 514 or use the port value that you configured for your remote syslog server
From the Facility Code list, select the syslog facility to use for logging events (for example LOCAL6)
For the select
Set the maximum length to
Selecting TCP Syslog and 8192 as the Maximum Message Length will help you avoid issues with field mappings.
Next, configure the Falcon LogScale Collector to ship the logs from your syslog server into LogScale. Follow Log Collector Install Falcon LogScale Collector and Configure Falcon LogScale Collector. Log Collector documentation also provides an example of how you can configure your syslog datasource, see Configuration Examples.
Verify Data is Arriving in LogScale
Once you have completed the above steps the data should be arriving in your LogScale repository.
You can verify this by doing a simple search for the events:
#Vendor = "cisco"
| #event.module="ise"Package Contents Explained
This package contains the following parser:
cisco-ise - a parser for Cisco ISE logs in the syslog format. More about log format can be found in Cisco documentation.
This package parses incoming data, and normalizing the data as part of that parsing. The parser normalizes the data to CrowdStrike Parsing Standard (CPS) 1.0 schema based on OpenTelemetry standards, while still preserving the original data.
If you want to search using the original field names and values, you can access those in the fields whose names are prefixed with the word Vendor. Fields which are not prefixed with Vendor are standard fields which are either based on the schema (for example, source.ip) or on LogScale conventions (@rawstring).
The fields which the parser currently maps the data to, are chosen based on what seems the most relevant, and will potentially be expanded in the future. But the parser won't necessarily normalize every field that has potential to be normalized.
Next steps and use cases
You can get actionable insights from your Cisco Identity Service Engine data by hunting for suspicious activity in LogScale using the search UI, dashboards or alerts.