Understanding Releases and Notes
Our release notes contain detailed information about each release, including:
Improvements — new features and functionality added or updated in the product
Bug Fixes — bug fixes addressing previous functionality
UI Changes — changes to the user interface
API Changes — changes to the APIs (REST or GraphQL) that may alter integrations
Configuration Changes — differences in the configurable settings
Upgrade Compatibility — basic release compatibility and advice for upgrades
Generally Available (GA) & Long Term Support (LTS) Releases
LogScale provides two separate releases:
Generally Available (GA) releases — includes new functionality. Using a GA release gets you access to the latest features and functionality.
GA releases are deployed in LogScale SaaS environments.
Long Term Support (LTS) releases — contains the latest features and functionality.
LogScale self-hosted customers are advised to install the LTS releases. LTS releases are provided approximately every six weeks.
Security fixes are applied to the last three LTS releases.
Internal or Not Released releases — are not released to customers, but included in the list to keep clarity for the version numbers.
LogScale SaaS/LogScale Cloud customers are upgraded on a staggered release schedule, with individual clusters being upgraded up to twice each month, using the corresponding latest GA release at the time of the upgrade.
Version Numbering
We follow a version numbering convention that is similar to that
recommended by Semantic
Versioning. Basically, we use the
MAJOR.MINOR.PATCH numbering format,
which is defined as follows:
MAJOR: When there are major changes to the software, including high-profile ones, we'll change the value of this number, the primary number (for example, the version will change from
1.x.xto2.x.x).MINOR: When we've added some new features or new functionality to LogScale software, we'll issue a new release and the secondary number will be changed (for example,
1.16to1.18). Unlike Semantic Versioning, though, we allow backwards incompatible changes (for example, changing compression algorithms).PATCH: When a patch is added, the tertiary or third number will be increased (for example,
1.18to1.18.1). Only backwards-compatible security or bug fixes are made with these. No new features or other code changes are permitted. This is important, as it means that each patch release should be more stable than the last.
Deprecation, Removal, and Breaking Changes
On occasion, changes to LogScale may need to be made that remove features or that are are considered Breaking Changes. These indicate significant changes to the operation of LogScale that are required to support new functionality or behavior or to ensure the security or reliability of LogScale. These include:
Changes to the current behaviour of a feature. For example, changing the way a function operates
Changes to the errors, responses or reactions to certain functions. For example, raising an error in place or a warning
Changing the format or compatibility of a file or file format
Removal of a feature or function
When an item that fits these criteria has been identified:
If the item is a deprecation (i.e. planned removal of functionality) then an item will be added to the release notes identifying the deprecation.
If the item is a breaking change, a Pre Warning entry will be added to the release notes, indicating the feature or functionality will be altered.
These deprecating or pre-warnings will be repeated in each release note version until the item has been changed or removed.
The corresponding documentation page will be updated with a deprecation or pre-warning message to highlight the upcoming change.
There will be a delay of at least 12 weeks between notification of the upcoming change and it being applied.
Once the item has been removed, a Removal release note entry will be provided indicating the removal, impact, and alternatives (if available).
Release Summary, Support, and Upgrade Requirements
When reviewing the release notes, a section at the top of each release notes sections provides basic information about the release and upgrade compatibility. For example:
| Version? | Type? | Release Date? | Availability? | End of Support | Security Updates? | Upgrades From? | Downgrades To? | Config. Changes? |
|---|---|---|---|---|---|---|---|---|
| 1.129.0 | GA | 2024-03-12 | Cloud | 2025-04-30 | No | 1.106.0 | 1.112.0 | No |
Version
The full version number for this release.
Type
The release type, either LTS or GA.
Release Date
The date when this version was released.
Availability
Where the version will be available:
Cloud— available to our cloud customersOn-Prem— available to our On-Prem and cloud customers
End of Support
The date when LogScale Support will no longer support this version.
Due to the release structure, this may show
Next LTS Versionwhich indicates that support will exist until the next full LTS release type is made available.Security Updates
Indicates whether the release will continue to get security updates.
Upgrades From
The minimum version of LogScale required to upgrade to this version. Upgrades from earlier versions may not succeed and are not recommended.
Important
For some releases, once upgraded to a the minimum upgrade release, it may not be possible to downgrade to a previous version. This will be shown in the corresponding release version when relevant.
Downgrades To
The maximum version of LogScale that you can downgrade to. Downgrading beyond this version may not work, or may corrupt data or the global database and may not be recoverable.
Minimum JDK Version
The compatible JDK version required to upgrade to this version.
Config. Changes
Indicates whether there are configuration changes within the release that should be checked and updated during the upgrade process to ensure that they meet your requirements.
Built-in Release Information
To determine the version of LogScale you are using and view information on the latest releases available from the LogScale user interface:
Click the caption icon at the top of the screen: the Releases panel shows the full list of releases, with the most recent on top.
Click any release link for all detailed information on that release.
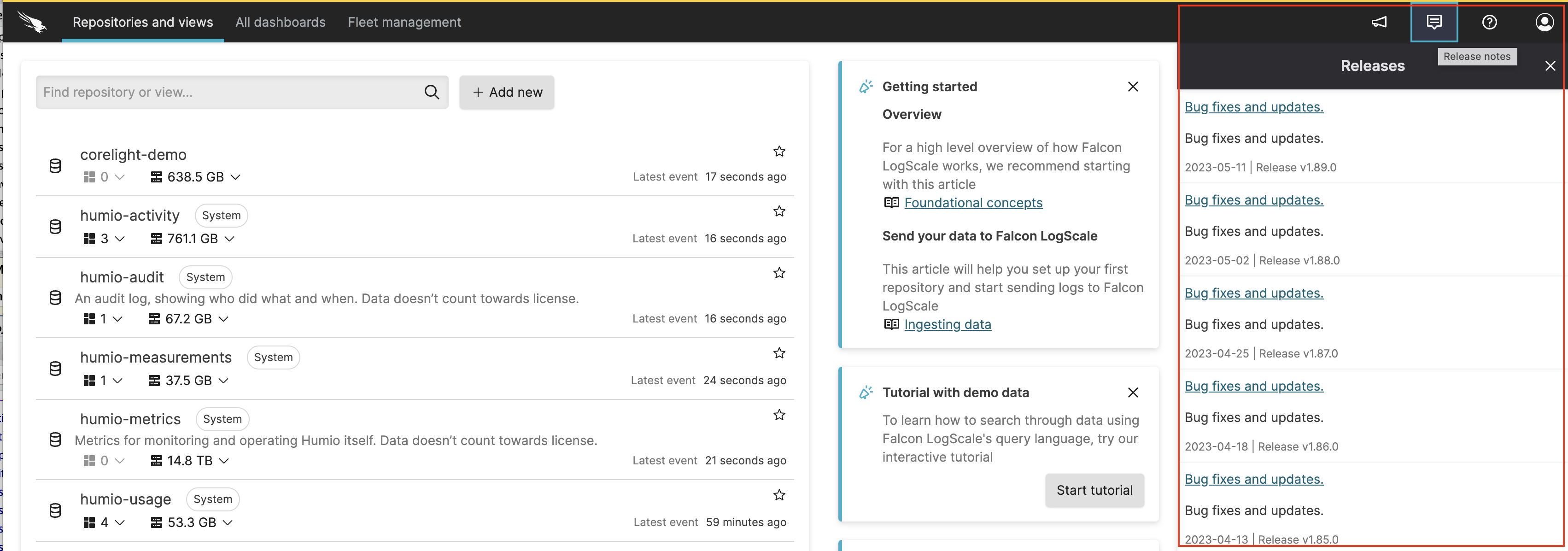 |
Figure 1. Built-in Release Information
Identifying Latest Releases
A file is generated that contains the current version information for LogScale builds to provide the latest GA and LTS release to be used during automations.
The file is available here: https://library.humio.com/release-notes/js/releases.json.
The file is JSON:
{
"GA" : "1.180.0",
"LTS" : "1.171.1"
}Searching Release Notes
Release Notes can be searched using a dedicated search interface: Search Release Notes.
Using the search system you can:
Search across a specific series of versions
Search for specific features or fuctionality using plain text
Filter by specific entry types (bug, improvement) and classes (deprecation, installation, security)
Searches automatically create a URL that can be used to share the search results and output with others.
Release Notes as RSS
An RSS version of the release notes is automatically built alongside the rest of the documentation. This information is used directly within LogScale to provide the RSS for releases in the UI.
The RSS file can also be accessed directly here: https://library.humio.com/release-notes/releasenotes-rss.xml.
Validating Release Checksums
The release notes include the checksum for release packages and Docker images. You can verify the checksum for a package on the command-line:
To check an MD5 hash use the md5 tool:
shell$md5 server-1.237.0.tar.gzMD5 (server-1.237.0.jar) = 4b4b4411d930d00275bc3a412c0c5c50To check an SHA hash, use the shasum command:
shell$shasum server-1.237.0.tar.gzca22652ca303a162f81711f43977e14e528f6e85 server-1.237.0.tarshellTo check an SHA256 hash, use the shasum command:
shell$shasum -a 256 server-1.237.0.tar.gz908a907b5c1ffbdce667b932daea0aab46a8ece4e164072f5bae0eb77d3bdd6f server-1.237.0.tarTo check an SHA512 hash, use the shasum command:
shell$shasum -a 512 server-1.237.0.tar.gzbbc65ea8641ac3d9910da4a9dcda0c1817d2a8acc2e81491a389d2671af7e57c12f019ad71af7309d4ad68b67997a6cbd3b0fba3a2048f07b7c7567abd05b8ae server-1.237.0.tar
To aid with automation, a file version of each hash is available in the
filehashes directory. For example, to obtain the
filehash for the SHA256 version:
$ wget https://library.humio.com/release-notes/filehashes/server-alpine-x64-1.237.0.sha256If the checksums do not match the quoted values, you should obtain a new version of the package.
Organization and Grouping
Release note entries are automatically structured according to their type (bug, feature, etc.) and their individual class (grouping), automatically sorted according to the priority of the entries, and marked up where appropriate to highlight entries that are more important or significant than others.
The two different groups are nested; first grouped by the issue type and then by class. For example, all bugs are listed together, and then groups of bugs related to the UI, or API, are grouped together.
The following types of release note, and their markup, are provided below:
Breaking Changes
Release note entry
Advance Warning
Release note entry
Removed
Release note entry
Deprecation
Release note entry
Behavior Changes
Release note entry
Upgrades
Release note entry
New features and improvements
Release note entry
Fixed in this release
Release note entry
Known Issues
Release note entry
Early Access
Release note entry
Improvement
Release note entry
Recent Package Updates
Release note entry
The following classes of release note entries are provided:
Security
Release note entry
Installation and Deployment
Release note entry
Administration and Management
Release note entry
Summary
Release note entry
Falcon Data Replicator
Release note entry
User Interface
Release note entry
Documentation
Release note entry
Automation and Triggers
Release note entry
GraphQL API
Release note entry
Storage
Release note entry
API
Release note entry
Configuration
Release note entry
Dashboards and Widgets
Release note entry
Ingestion
Release note entry
Log Collector
Release note entry
Queries
Release note entry
Fleet Management
Release note entry
Metrics and Monitoring
Release note entry
Auditing and Monitoring
Release note entry
Functions
Release note entry
Other
Release note entry
Packages
Release note entry
Package Changes
Release note entry