
Cisco Meraki
The parser normalizes MX Security Appliances and
MR Access Points data.
Breaking Changes
This update includes parser changes, which means that data ingested after upgrade will not be backwards compatible with logs ingested with the previous version.
Updating to version 1.0.0 or newer will therefore result in issues with existing queries in for example dashboards or alerts created prior to this version.
See CrowdStrike Parsing Standard (CPS) 1.0 for more details on the new parser schema.
Follow the CPS Migration to update your queries to use the fields and tags that are available in data parsed with version 1.0.0.
Installing the Package in LogScale
Find the repository where you want to send the Cisco Meraki events, or create a new one.
Navigate to your repository in the LogScale interface, click Settings and then on the left.
Click and install the LogScale package for Cisco Meraki (i.e. cisco/meraki).
When the package has finished installing, click on the left (still under the , see Figure 20, “Ingest Token”).
In the right panel, click to create a new token. Give the token an appropriate name (e.g. the name of the server the token is ingesting logs for), and either leave the parser unassigned (instead of setting the parser in the log collector configuration later on), or assign the
cisco-merakiparser to it.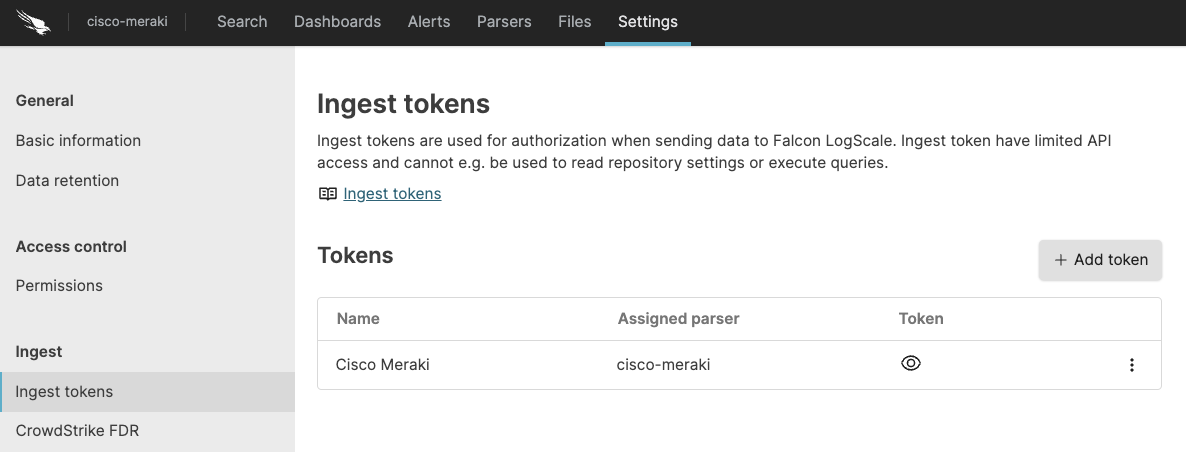
Figure 20. Ingest Token
Before leaving this page, view the ingest token and copy it to your clipboard — to save it temporarily elsewhere.
Configure the syslog server to send the Cisco Meraki events to LogScale.
Now that you have a repository set up in LogScale along with an ingest token you're ready to send logs to LogScale.
For more about Cisco Meraki event types and configuration, visit the Syslog Event Types and Log Samples and the Syslog Server Overview and Configuration pages.
Verify Data is Arriving in LogScale
Once you have completed the above steps the Cisco Meraki data should be arriving in your LogScale repository.
You can verify this by doing a simple search for the events:
#Vendor = "cisco"
| #event.module = "meraki"Package Contents Explained
This package parses incoming data, and normalizing the data as part of that parsing. The parser normalizes the data to CrowdStrike Parsing Standard (CPS) 1.0 schema based on OpenTelemetry standards, while still preserving the original data.
If you want to search using the original field names and values, you can access those in the fields whose names are prefixed with the word "Vendor". Fields which are not prefixed with "Vendor" are standard fields which are either based on the schema (e.g. source.ip) or on LogScale conventions (e.g. @rawstring).
The fields which the parser currently maps the data to, are chosen based on what seems the most relevant, and will potentially be expanded in the future. But the parser won't necessarily normalize every field that has potential to be normalized.
Event Categorisation
As part of the schema, events are categorized by four different fields:
event.category
event.type
event.category and event.type are arrays, so need to be searched like so:
array:contains("event.category[]", value="network")
This will find events where some event.category[n] field contains the value "network", regardless of what `n` is. Note that not all events will be categorized to this level of detail.
Normalized Fields
Here are some of the normalized fields which are being set by this parser:
source.* (e.g. source.address)
network.* (e.g. network.direction)
destination.* (e.g. destination.ip, destination.port)
threat.* (e.g. threat.indicator)