Terraform Sequence
Terraform Deployment Sequence (Repo-Specific)
This repo is opinionated about apply order because
module.logscale contains
kubernetes_manifest resources that require CRDs to
exist at plan time. The practical result
is that you must apply CRDs
first.
Workspace validation: Each tfvars file
includes workspace_name which
must match
terraform.workspace; a mismatch triggers a warning to
prevent applying the wrong configuration.
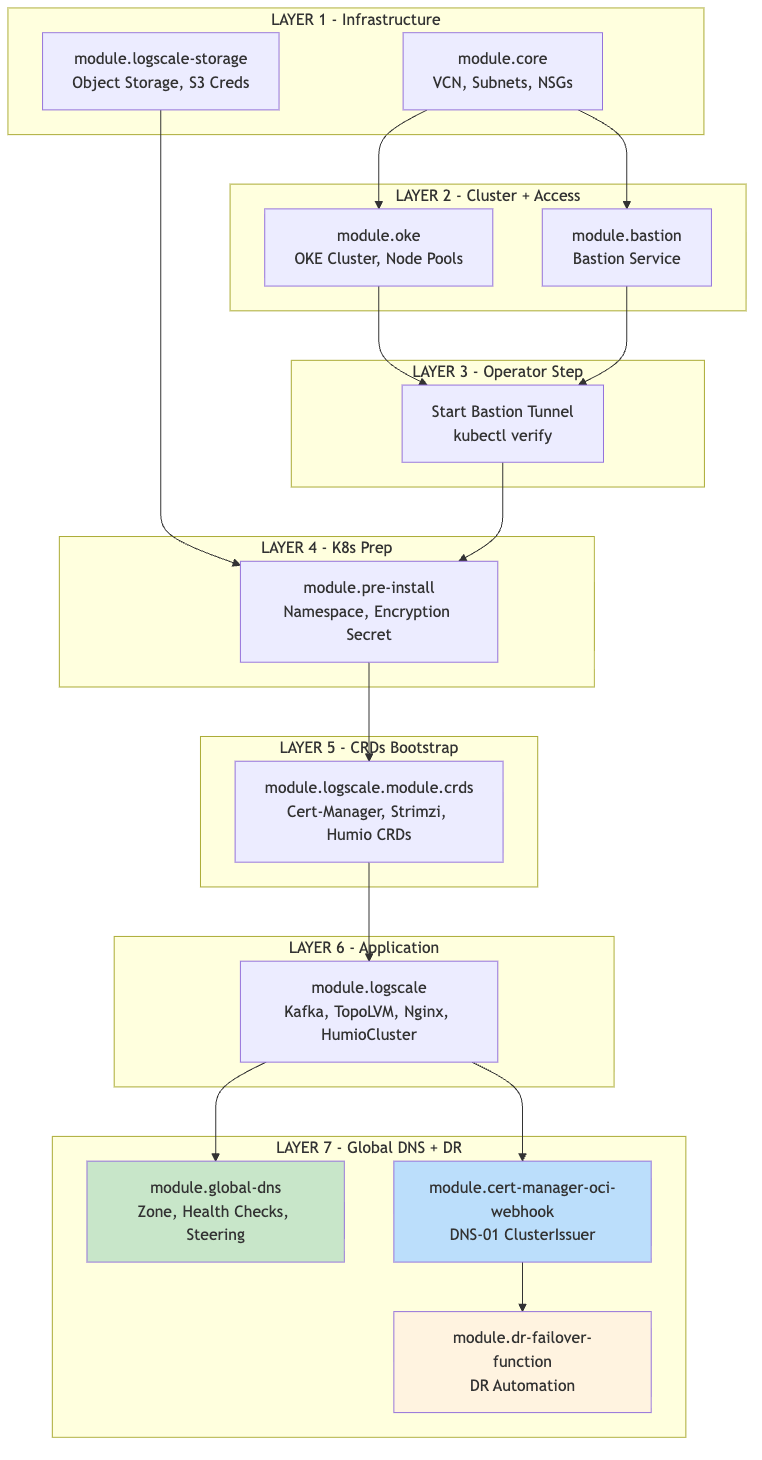
Follow this order to apply Terraform safely and avoid dependency issues.
Each module references outputs from upstream modules. The diagram below shows the dependency order — modules must be deployed top-to-bottom. Deploying out of order will result in missing references or Terraform errors.
Note
module.oci-logscale-storage feeds into
module.pre-install because the storage module creates
the Object Storage bucket and S3-compatible credentials, which the
pre-install module needs to create the storage encryption Kubernetes
secret. When both modules are included in the same targeted apply
(-target), Terraform resolves this dependency
automatically.
 |
Important: Steps 4-7 require an active
bastion tunnel and kubectl access to the OKE cluster.
The module.logscale module contains
kubernetes_manifest resources that require the
Kubernetes API to be reachable at plan time, not just apply time.
Before running terraform plan or terraform apply for these modules:
Ensure that your bastion tunnel is running
Set
kubernetes_api_hostcorrectly (e.g.,https://127.0.0.1:16443for primary,https://127.0.0.1:16444for secondary)Set the kubectl context to the target OKE cluster (kubectl config use-context oci-primary or kubectl config use-context oci-secondary)
Important: The DNS-01 webhook module should be applied on both primary and secondary clusters when:
public_lb_cidrsrestricts port 80/443 (recommended for security), blocking Let's Encrypt HTTP-01 validation, and/or:the standby cluster already has the global FQDN certificate ready before failover
With cert_dns01_webhook_mode="auto", the module deploys only
when DNS-01 is likely required (based on
public_lb_cidrs and DR standby/global-FQDN conditions).