Failover Function Security
The DR failover Azure Function is secured with multiple layers:
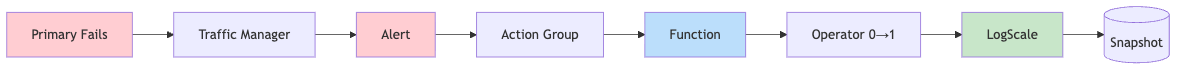
Azure Function Failover Chain
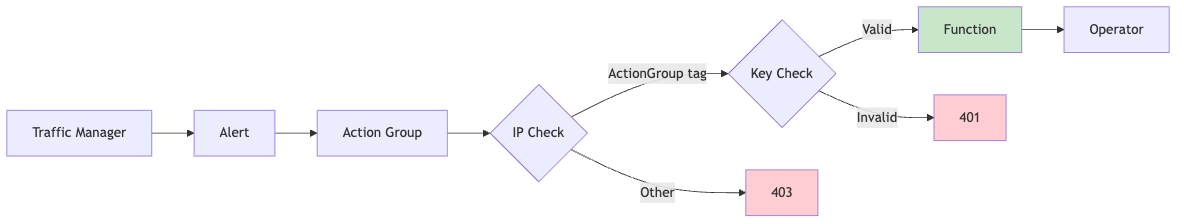
Security Architecture
Security Controls
Function App Outbound IPs and AKS Access
These are described in the following sections.
Azure Function Failover Chain
 |
Security architecture
 |
Security controls
| Layer | Control | Configuration | Purpose |
|---|---|---|---|
| Network | IP Restriction | ip_restriction_default_action = "Deny" | Deny all traffic by default |
| Network | Service Tag Allow | service_tag = "ActionGroup" | Only Azure Monitor Action Groups |
| Transport | HTTPS Only | https_only = true | Enforce encrypted connections |
| Transport | TLS 1.2 Minimum | minimum_tls_version = "1.2" | Prevent downgrade attacks |
| Application | Function Key | auth_level = FUNCTION | Require function key in URL |
Function App Outbound IPs and AKS Access
When AKS is configured with authorized IP ranges, the Function App's outbound IPs must be included. This is handled automatically by Terraform.
Troubleshooting Function App connectivity
If the Function App logs show connection timeout errors:
text
Connection to <aks-cluster>.hcp.<region>.azmk8s.io timed outVerify the function's outbound IPs are in the AKS authorized ranges:
shell
# Get Function App outbound IPs
az functionapp show \
--name <function-app-name> \
--resource-group <rg-name> \
--query "possibleOutboundIpAddresses" -o tsv | tr ',' '\n'
# Get AKS authorized IP ranges
az aks show \
--name <aks-cluster-name> \
--resource-group <rg-name> \
--query "apiServerAccessProfile.authorizedIpRanges" -o tsv