cert-manager OCI Webhook (module.cert-manager-oci-webhook)
Purpose: Optional. Issues TLS certificates via DNS-01 validation when the operator does not provide their own certificate and the cluster is not internet-accessible.
This module is needed when both of these conditions are true:
The operator does not bring their own TLS certificate
The cluster is not reachable from the internet. Firewall rules (
public_lb_cidrs) block port 80, or the DR standby cluster needs the certificate issued before failover when no traffic is routed to it yet.
Deployed on: Any workspace with
cert_dns01_provider="oci" and
cert_dns01_webhook_enabled=true when DNS-01 is needed.
This diagram shows how Terraform provisions the webhook resources and how the runtime certificate issuance flow works end-to-end using DNS-01 validation:
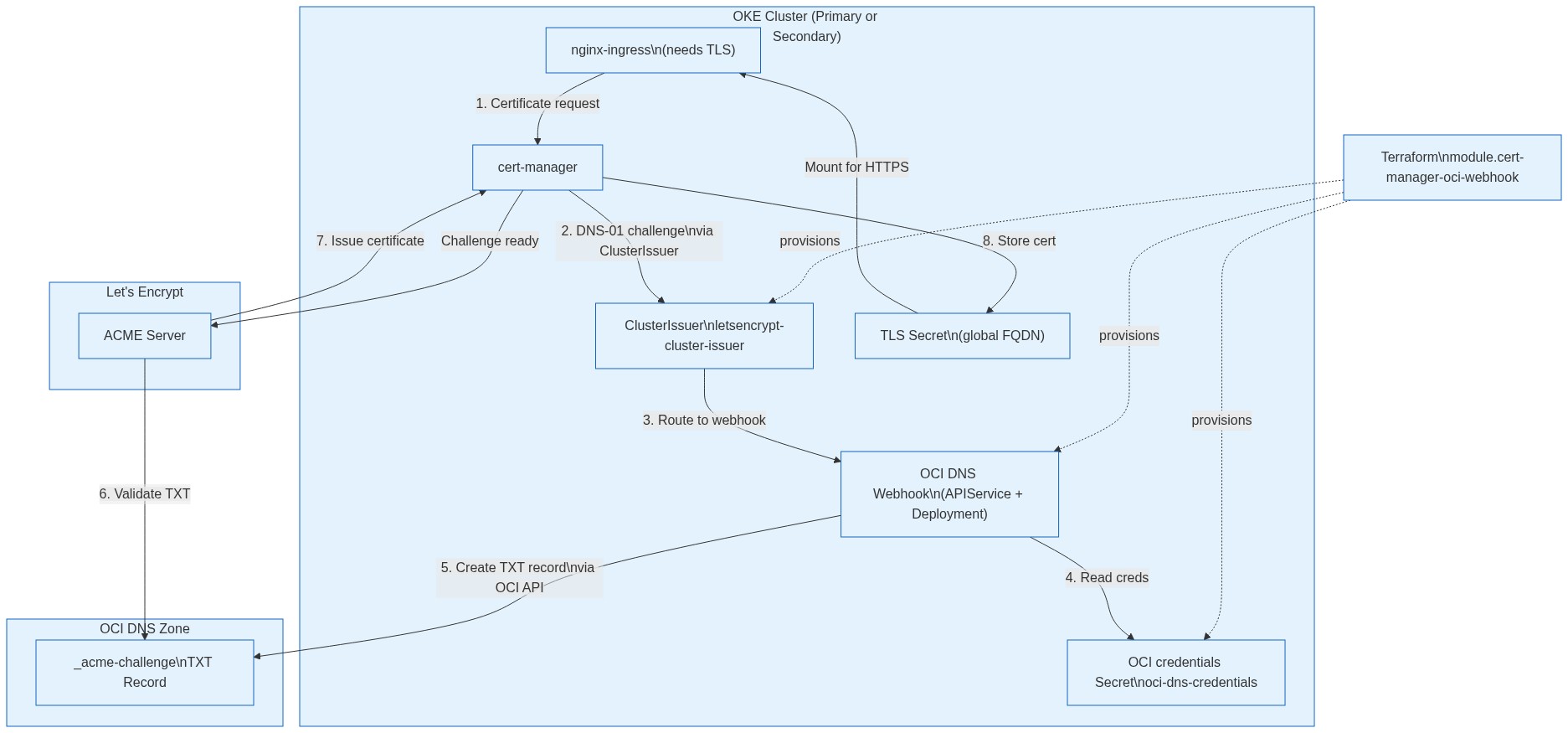 |
Step by step certificate flow:
| Step | Component | Action |
|---|---|---|
| 1 | Ingress | Annotation triggers cert-manager to request a certificate |
| 2 | cert-manager | Creates ACME Order with DNS-01 challenge type |
| 3 | ClusterIssuer | Routes challenge to OCI DNS webhook via APIService |
| 4 | Webhook |
Reads OCI API credentials from
oci-dns-credentials secret
|
| 5 | Webhook |
Creates _acme-challenge.{domain} TXT record in
OCI DNS
|
| 6 | Let's Encrypt | Queries DNS, finds the token, validates domain ownership |
| 7 | cert-manager | Stores issued certificate in Kubernetes Secret |
| 8 | Webhook | Removes the challenge TXT record (cleanup) |
HTTP-01 vs DNS-01 Comparison:
| Aspect | HTTP-01 | DNS-01 (Webhook) |
|---|---|---|
| Strimzi Kafka cluster | Must allow Let's Encrypt IPs to port 80 | No inbound access needed |
| Humio operator | Required | Not required |
| HumioCluster CR | Not supported | Supported |
| nginx-ingress | May fail during DNS switch | Works anytime |
| cert-manager | Simple | Requires webhook + OCI credentials |
Configuration (tfvars):
cert_dns01_provider = "oci"
cert_dns01_webhook_enabled = true
cert_dns01_webhook_mode = "auto" # or "always"